AMD-SB-7005 “Return Address Security Bulletin” outlines this new speculative side channel attack affecting recent EPYC and Ryzen processors.
AMD has received an external report titled ‘INCEPTION’, describing a new speculative side channel attack. AMD believes ‘Inception’ is only potentially exploitable locally, such as via downloaded malware, and recommends customers employ security best practices, including running up-to-date software and malware detection tools. AMD is not aware of any exploit of ‘Inception’ outside the research environment, at this time.
Oh hey, a non-Intel speculative execution vulnerability.
I’ve been wondering whether speculative execution as it’s currently done is just fundamentally broken and guaranteed to leak information one way or another, but I really don’t know enough about CPU design to even make a guess
It was done to do the both side of if/else while waiting for the check to finish, then it jumps to the correct branch result execution point to keep going, whatever that was “wrong” is wasted and should be flushed. Don’t know if this fits the modern definition but that’s why they do this type of thing.
Actual design or implementation is more complex than I described as there are a couple ways to tackle this branching delay issue.
Does it execute both, or does it execute the branch that is more likely to be valid? Branch prediction seems like it’d be way more performant than executing both branches until the result of the branch condition is available. If you think about it, what you’re proposing will cause the CPU to always execute instructions that are not meant to be executed when confronted with a branch whereas branch prediction will only execute these “useless” instructions in the unlikely scenario where the prediction is incorrect.
It will prefetch the instructions and put into the pipeline the branch it thinks is mostly likely. It may do ahead-of-time speculative execution on certain instructions but not always. If it missed the correct branch it will flush the pipeline and start the pipeline over again from the correct branch. Afaik it doesn’t execute or prefetch both branches. The other guy is saying it does but that doesn’t really gel with my own recollection or the Wikipedia article he cited. You can see some further discussion that suggests only one branch gets prefetched here here and here. Reasons cited for only predicting one branch are: 1) Two pipelines with all the associated circuitry to look ahead, decode, and speculatively execute is incredibly expensive in terms of both processing requirements and die real estate. 2) Caching both would thrash your caches with new data constantly. 3) Modern branch prediction is already so accurate, there’s really no need for two pipelines anyways.
Maybe CPU manufactures shouldn’t add hacks to their CPUs for more performance, and therefore more $$$'s. If they were held liable this’d never happen.
Do you know why Zen 2 and Zen 1 don’t have this issue? Because they didn’t come up with the hack they used to increase performance (and therefore $$$'s) back then because they knew it’d leak like crazy. This time it didn’t seem like they cared.
How is getting more performance out of a CPU greedy? Is making a better product that people want greedy? Stagnation is lazy, and making CPUs faster is better for the consumer. So is AMD putting pressure on Intel by releasing faster and faster CPUs. This is a large part of why we have such powerful computers now that shape our modern world.
What “hack” are you talking about that they implemented in Zen 3? Speculative Execution has been around for years, and speculative execution vulnerabilities have been happening ever since. Thankfully, the fix is available and not incredibly difficult to implement, which seems to be the case for most of these bugs. Why should we sacrifice speed for the potential that maybe we implement a bug that can be fixed with a BIOS upgrade?
Getting more performance is not greedy. What is greedy is adding hacks for performance for $$$'s which is greedy considering the security nightmares that come with it. Also, how the hell are you supposed to update your BIOS if it’s not supported by
fwupdand you can’t use Windows?Also, what Zen 3 added was not flushing what Zen 2 flushed.
🤖 I’m a bot that provides automatic summaries for articles:
Click here to see the summary
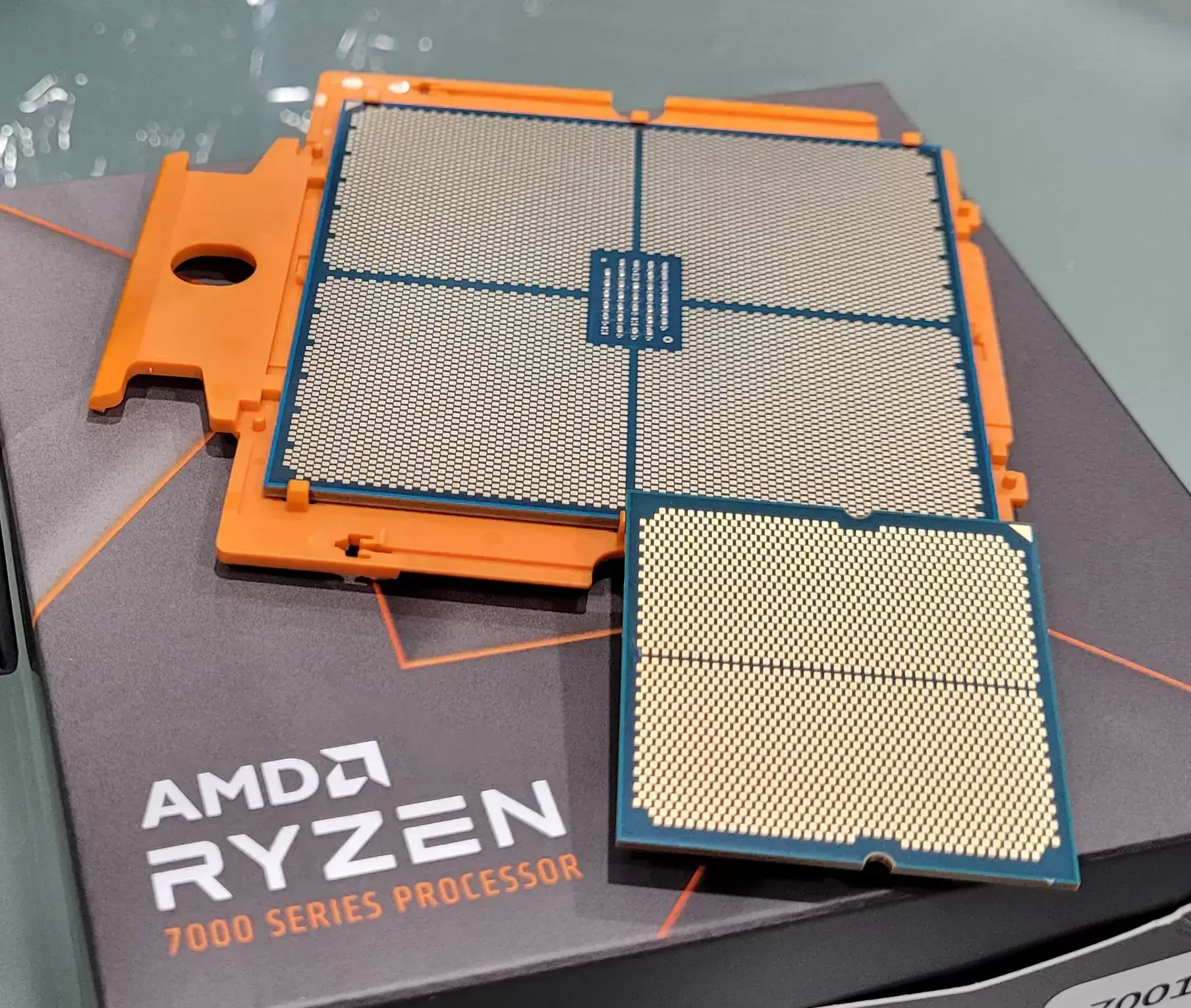
AMD has kicked off a busy Patch Tuesday by disclosing INCEPTION, a new speculative side channel attack affecting Zen 3 and Zen 4 processors.
AMD-SB-7005 “Return Address Security Bulletin” outlines this new speculative side channel attack affecting recent EPYC and Ryzen processors.
AMD believes ‘Inception’ is only potentially exploitable locally, such as via downloaded malware, and recommends customers employ security best practices, including running up-to-date software and malware detection tools.
AMD is not aware of any exploit of ‘Inception’ outside the research environment, at this time.
No µcode patch or BIOS update is necessary for products based on “Zen” or “Zen 2” CPU architectures because these architectures are already designed to flush branch type predictions from the branch predictor.
Please refer to your OEM, ODM or motherboard manufacturer for a BIOS update specific to your product.
@rikudou@lemmings.world Seems the bot does duplicates sometimes, might want to look into that.
I will, thanks for the report!
Bad bot ☹️